What is the security concerns for low code and no code development? Low code and no-code technology allows your online database to be built with a user-friendly drag and drop format. This is far easier than creating raw code from scratch. There is minimal or no hand coding used. Consequently, technical and non-technical online application builders can construct the application faster and more efficiently. Further down the line, modifications can also be done without engaging a software developer. This saves time and money. But what’s the impact on low code security for your precious data?

The impact of low code security for your business data
Custom made online databases or other web apps can produce a minefield of vulnerable code. This is a serious risk to your business or organization.
If deployed into production, this would require the vulnerabilities to be found ASAP and plugged. Frantically putting fixes in place is highly risky as hackers can access exposed data.
Many out of the box or off the shelf solutions should present a lower risk than fully bespoke software. However, off the shelf software may not easily support your specific business processes. Data protection is critical to your business while a fit for purpose online database is important too. Cost effective customizations means you don’t have to shoehorn your business requirements into an off the shelf solution. But new customized code could be increasing your security risk.
Security for low code and no-code platform
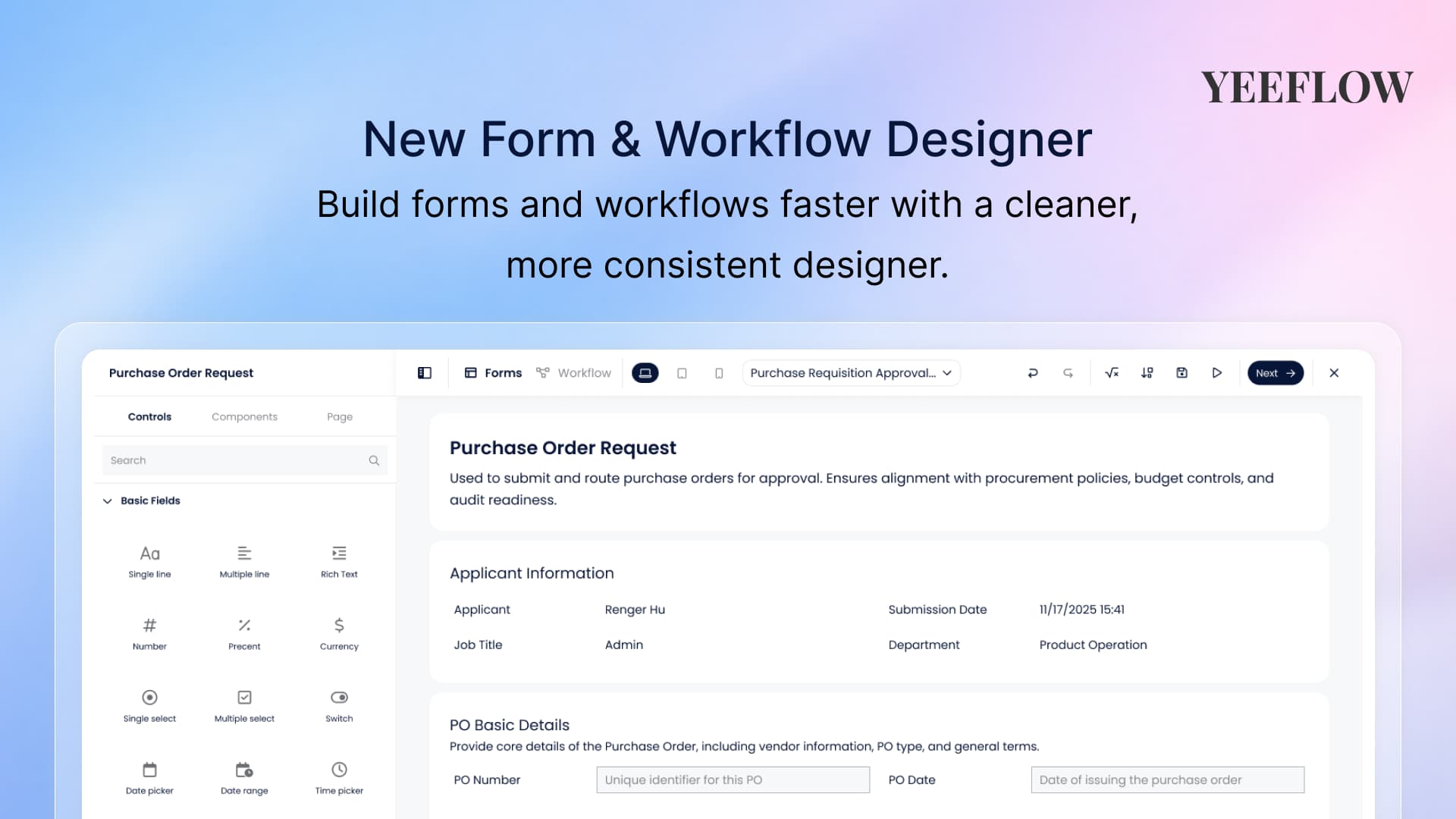
Low code platforms, such as Yeeflow, are developed with a model of secure application security covering architecture design, implementation, and testing. Robust low code platforms have been tried, tested and are continuously monitored. Security is a major consideration from the onset and is a foundation stone of the platform. Critically, security testing has been done early in the software delivery lifecycle and continuously iterated. Not at the end when the project is pushed for time and security has been relegated to the bottom of the priority list.

Proven secure application deployment processes used in the development life cycle reduce risk.
This includes enforcement of HTTPS/SSL encryption, access control and auditing. There are low code solutions that allow client builders to expose data inadvertently. For example, when application solution provider or online form builders do not easily understand the security model. When choosing a product check the low code platform has a UI that informs builders their data is collected and kept in the state as intended. For example, having a building UI that clearly defines authorized levels of data access. Alternatively, ask the supplier to carry out audits covering data protection.
The security concerns for low-code no-code apps that need to be considered by every enterprise.
Where is the platform running on?
Firstly, as the user of the low-code and no-code platform, you need to know where the platform is running on. Like the locations of the cloud servers and the backend provider of those infrastructure, which is called Cloud Service Provider (CSP). If the platform is running on an unknown or non-famous IaaS provider, you might be under a high risk of the security protection. The big players in the cloud service sphere include Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP).
Like for Yeeflow, the platform is built on Microsoft Azure, one of the most popular cloud platform, especially for business and enterprise users. Why are enterprises entrusting their business data and applications with Microsoft Azure cloud storage? What makes them a favored choice among businesses?

Microsoft guarantees the best security and protection for all the data held on the Azure cloud. In addition to its standard security model of Detect, Assess, Diagnose, Stabilize and Close, the cloud platform also meets international industry-specific standards such as ISO 27001 and HIPAA. Leveraging its decades of enterprise software experience, Microsoft always make it a point to improve its security offerings of Azure. Not only is it the most trusted cloud platform by U.S government institutions, but Azure also meets a number of country-specific standards such as UK’s G-Cloud and Australia’s IRAP. What is more is that it is the first CSP to embrace the new international standard for cloud privacy — ISO 27018. Multi-level protection, multiple compliance certifications, cybersecurity controls and threat mitigation practices of Microsoft Azure management ensures a higher level of security within the cloud environment.
How to protect the users authentication and authorization?
There are two main security concepts when accessing data in the low-code and no-code platform:
- authentication: determines the identity of the caller
- authorization: determines which actions the caller can take
The identity of your app or integration is taken as the user involved in the authentication process. The actions the app or integration can take are controlled by that user’s permissions.
Yeeflow supports OAuth-based sign in for Google and Office 365 accounts. There is also a custom Single sign on (SSO) option for organizations using a SAML-based sign in (useful if you are using Okta, OneLogin, etc.) From the Sign in Options section, you can restrict the options available for signing in.
Multi-factor authentication increases the security of user logins for cloud services above and beyond just a password. With the integration with Office 365, Yeeflow can leverage the features of Multi-Factor Authentication form Office 365. This allows organizations with these subscriptions to enable multi-factor authentication for their Office 365 users without requiring any additional purchase or subscription.
What kind of security management provided by the platform?
Low code and no code development platforms typically include permissions and access controls by default, often inherited from the underlying data they hold for their customers. That can make it easier for both experienced developers and non-developers to quickly create secure apps.
But managing the complexities of security administration is one of the growing concerns in any enterprise, especially those open to e-commerce and those with large networks. In such demanding times, the availability of Security Management is considered predominant – affecting all sectors of an enterprise. The foundation of any security management is a model with role-based access control, enabling all the required functionality and authentication for a security system. Role-based access control (also known as role-based security) is a method of managing authorization while performing tasks in complex systems – many users and many resources.
Yeeflow provides an Enterprise-grade Role-based security with a defined set of permissions and hierarchical accessibility.
- Manage Users – Manage all the users in your Yeeflow account, deactivate users who are no longer part of the company account.
- Manage Profiles – Create profiles that define the access permissions for the users. Set module-level and feature-level permissions for different profiles.
- Manage Roles – Create roles for the users in your account such as CEO, Sales Manager, Marketing Manager etc.
- Field Permissions – Control the access rights of creator fields and link for various profiles.
- Domain Restriction – Restrict access only to the users whose email addresses belong to the verified domain.
- Advanced Sharing Settings – Define rules that help you to share data with peers, management, and subordinates.
Now that you see how secure low-code can be, learn more about Yeeflow enterprise-class features, including security, on our website.





.png)
